Compression History Discovery through Video Range Decoding for Fake Video Detection
The Research Foundation – Flanders (FWO)
The objective of FWO’s Research projects is to advance fundamental scientific research. FWO has granted our research project proposal for the 2022 call for proposals. The proposal was one out of only two granted projects in the Junior research projects call in the Informatics and Knowledge Technology panel. Over all the different fields of research (biological sciences, humanities, social sciences, medical sciences, science and technology, and interdisciplinary), 79 proposals have been granted 4-year funding.
Fact checking manipulated images is particularly challenging
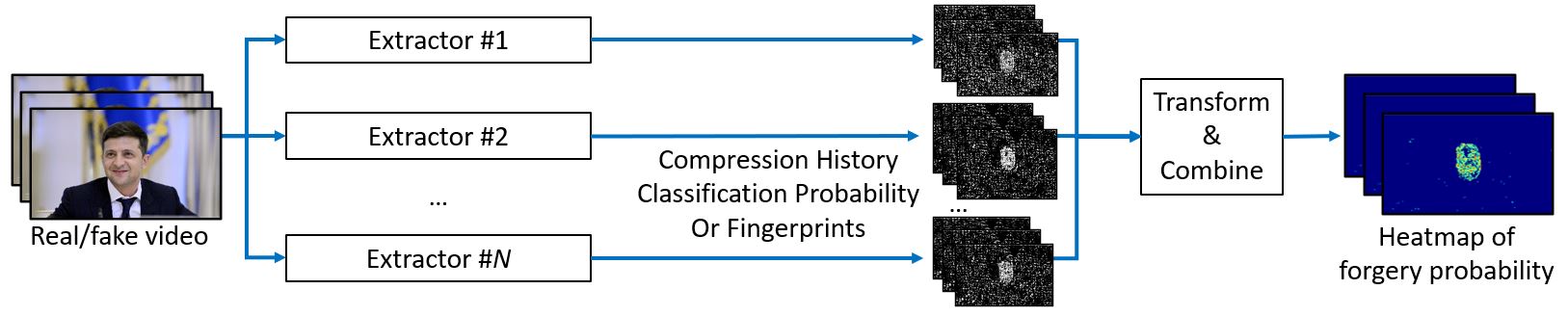
To detect manipulation, we exploit “compression history fingerprints”. This concept considers that fake regions typically underwent a different amount of compression steps, e.g., if a fake face was added to a video, then real regions are compressed twice, while fake regions are compressed once. Hence, manipulations are revealed by detecting inconsistencies in the traces of compression.
Especially the last video compression step has the potential to reveal more information about the video’s origin than what is retrieved in the state of the art. In this project, we propose a video range decoder that not only decodes the last compression step, but also provides the range of values in which the encoded video sample values are located.
We envision to overcome the two main limitations of the state of the art:.
- Lack of generalization:The proposal is not limited to a single type of forgery, but generalizes to forgeries found in the wild.
- Robustness: Better robustness against recompression attacks is achieved by using a variety of strategies. Our research demonstrated great robustness in compression artifacts, which indicates a high potential for the proposed approach.
How it works
In general, forensic methods look for inconsistencies in the traces of its digital history. Every step in the camera acquisition and editing process leaves a trail of clues. For example, the sensor of a camera introduces a unique noise pattern, and traditional compression introduces blocking artifacts. These traces are typically invisible to the human eye, but detectable by a computer. Hence, forensic methods exploit these imperceptible traces to detect forgeries. Unfortunately, these traces are often deleted when recompressed to a lower quality, as is done automatically when uploaded to social media. Additionally, most existing forensic methods are made for images, and the temporal domain in video-based forgeries is not yet fully explored.